The Patch Insights Administrator
Patch Insights Administrator - Introduction
The Patch Insights Administrator role is envisaged to use Patch Insights to complete the last mile patching of the estate. And so would following the environment's planned patching strategy use Patch Insights to:
Can check the patch logs on devices in real time.
Archive patches that are not of interest.
Complete patch deployment on those final devices that the main patching process has failed to reach, or where patches have failed for any reason.
Reboot devices where the patching strategy has not managed to reboot them, the Patch Insights Administrator will need to be aware of any maintenance windows and restrictions on device reboots.
Remember that Patch Insights is not a replacement for your patching process, the deployment to rings or the agreed timescales for rebooting of devices following patching. It does not in this iteration perform any remediation. Therefore, you will still have to investigate and rectify the reason for the failure prior to redeployment of the failing or missing patches.
Checking patch status - The Patch Screens
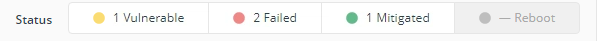
As part of their post patch deployment cycle, the Patch Insights Administrator opens Patch Insights and views the Patches page, with the plan of reviewing in turn the number of vulnerabilities, failures, mitigations and outstanding reboots.
Remove Patches not deployed via the environment patching solution
Prior to carrying out the redeployment of any patches, the Patch Insights Administrator should archive any patches listed in Patch Insights that have not been deployed via their patching solution, thus reducing the number of patches listed that would otherwise need to be checked and remediated.
The Patch Insights Administrator should slide the toggle for Include archived so that any archived patches are not displayed. Archived patches will remain hidden from view until either the slider is moved back to display all patches or the patch is removed from the Archive.
They then carry out a comparison between the patches deployed from the patching solution and Patch Insights selecting the archive option on any patches that have not been targeted at devices. When only patches that have been deployed are visible then the Patch Insights Administrator can carry out the following tasks, knowing that the patches listed have been deployed and are of interest.
Check and resolve Vulnerabilities
The Patch Insights Administrator views the status column, scrolling through checking for the highest number of vulnerabilities, once they find this they click on theVulnerable item in the Status row, which displays the list of devices that are reporting being vulnerable and requiring this patch.
The Patch Insights Administrator, could then select an individual device or multi select devices to be targeted. The Deploy Patch, Explore and Reboot buttons would then become enabled.
Deploy Patch allows the patch to be deployed to the selected devices.
Explore allows any Instructions the Patch Insights Administrator is permissioned to access to be run against the selected device(s) byUsing 1E Endpoint Troubleshooting .
Reboot allows the selected devices to be rebooted, each of these will be looked at in turn.
In this case with no errors showing the Deploy Patch button is clicked, the Confirmation pop up is displayed, with the option to select your preferred method of deployment. The options currently are:
SCCM.
WSUSR.
WSUSL.
There is no validation at this stage that a valid selection has been made, the instruction if run will fail on any machine were an invalid deployment method is selected.
Warning
Ensure that only methods configured for all the selected devices are selected in the drop list
Warning
There is no validation at this stage that a valid selection has been made, the instruction if run will fail on any machine were an invalid deployment method is selected.
After checking Deploy is then clicked and a user who is assigned to All Instructions Approver will need to approve the deployment of this Patch to the selected devices. They will receive email notification, and also in the 1E Endpoint Troubleshooting application an entry will be shown in the notifications page.
Warning
The Deploy patch option does not respect any patching rules or local rules, it will deploy the patch immediately, you MUST ensure you abide by local patching rules.
The approver clicks on the notification, reads the details and if they are happy with the information select the I understand the impact of this instruction and approve the request checkbox, followed by clicking the Approve button.
The instruction then runs on the selected devices. Its status can be checked by the Patch Insights Administrator in the 1E Endpoint Troubleshooting application, after changing the Consumer to Patch Insights in the drop list at the top of the screen. The instruction runs for 14400 seconds (4 hours) so that devices have a long period to install the patches.
The Patch Insights Administrator would repeat this for all vulnerabilities showing on the environment, against devices where a patch had been targeted and the required installation date has passed but the device still shows vulnerable.
Check and resolve Failures
The Patch Insights Administrator has now resolved all those patches showing as having a vulnerability, they can now move to action any patches that show as failed. Selecting the Highest patching failures in the Sort by drop list, the page refreshes and the patches are re listed with the highest number of failures listed first. Remember to check that the Include archived toggle is still showing those patches not archived.
With the patches sorted by number of failures, they click on the Failed item in the Status row. Which opens the patches screen, in the Details column the failure reason is shown.
Clicking on this shows the Event log for the device selected and the patch currently displayed. With an option to download the full event history to a .tsv file, this is the recommended way to view the full event history of the patch on the device.
The Patch Insights Administrator should then use this ErrorCode, and investigate the cause and solution for this error, and once the cause has been resolved, the patch can then be re deployed, by selecting the affected devices, and choosing Deploy Patch, and following the same process as shown in the Vulnerabilities section.
Mitigated devices
The Mitigated status means that the device has successfully patched, either directly via your patching solution, or the Patch Insights Administrator has deployed a Vulnerable patch or remediated a failing patch and re deployed it.
Reboot devices
The final status is that of reboot, and this shows those devices where a reboot is pending. Before using this, you should confirm that you will be abiding by any local rules in place for when devices can be rebooted, and you may want to use the filter options to only display devices in specific management groups to ensure you do not accidentally reboot a machine that has a VIP or special rules on when it can be rebooted.
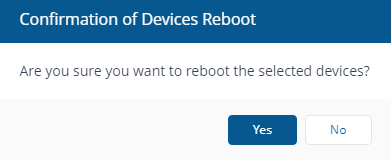
The Patch Insights Administrator identifies devices that require rebooting and are permitted to be rebooted at this point in time, and chooses the Reboot tile in the Status section, and selects the devices to be rebooted, the Reboot button enables, as we have seen for Deploy Patch and Explore, They click on the Reboot button and the Confirmation of Devices Reboot popup is displayed with Yes or No buttons enabled. They decide they do want to reboot the selected devices and are permitted by local rules to do so. And click Yes
The Reboot initiated - pending approval dialog is displayed. The Patch Insights Administrator has to provide the Authentication code as before and then a user with the All Instructions Approver role has to approve the instruction.
The approver gets the notification, notes that it lists the FQDN of the devices and that they will reboot in 90 seconds of the instruction arriving on the device. They select I understand the impact of this instruction and approve this request, the Approve button becomes enabled and is clicked. The devices are then rebooted.
The Patch Insights Administrator has now viewed via the Patches screen all the statuses of the patches on the estate and taken action, they could though have done this on a device basis using the Devices screen and this will be looked at now.
Checking patch status - The Device Screens
As part of their post patch deployment cycle, the Patch Insights Administrator opens Patch Insights and views the Devices page, with the plan of reviewing in turn the number of vulnerabilities, failures, mitigations and outstanding reboots.
The Patch Insights Administrator opens Patch Insights and navigates to Devices, the screen is displayed listing all devices known to 1E. The table shows the FQDN, Last Seen, Primary User, Vulnerabilities, Failures, Mitigations and Requires Reboot, with an Explore and Reboot button, which become enabled when a device is selected. This functionality was looked at previously.
Selecting the FQDN of the machine with the highest number of failures (which is a column that can be sorted ascending or descending) opens the Device view, which opens on the Patch Insights tab. (The other tabs may display data depending on the other roles the user has assigned to them, the detail of how these are populated is here: The Device View Overview tab )
From this view clicking on a link in the KB number column opens the Patches page with the information for all devices targeted by that Patch. The functionality here was looked at previously.
Clicking on the link in the Details column shows the Logs for the selected device and Patch, this was also looked at previously.
Selecting a row on the Device view page enabled the Deploy Patch button, again we have looked at this functionality previously. Finally the Explore button on this page is enabled in the top right of the screen, which will allow the Patch Insights Administrator to run any instructions they are permissioned to run.