Communication ports
Diagrams and tables with all the external Nomad communication ports. Useful, if needed, for network and device firewalls.
Networking
Due to the nature of how proxy servers can be implemented, some of which can be quite complex, you may need to consult your networking specialist to see if exceptions need to be added to enable Nomad’s peer-copy over HTTP or HTTPS.
The following are the ports used by Nomad client on clients and on Distribution Points. The table does not include Configuration Manager communications, which can be found here: https://docs.microsoft.com/en-us/sccm/core/plan-design/hierarchy/communications-between-endpoints.
Ports | Notes | Configurable |
|---|---|---|
UDP 1779 | Default port Nomad uses for listening to elections to determine the master on a subnet, control traffic and for content transfer if you have Connectionless enabled. A firewall exception must exist for this port. Nomad will create one automatically for Windows firewall, but not for other firewall software. | Yes, during installation. |
TCP 80 (HTTP) or TCP 443 (HTTPS) | Used when the Nomad master requests LSZ files from Nomad running on the DP and when the Nomad master downloads content using Nomad as provider. Communications depend on how the DP is configured. Configuration Manager is configured to use either HTTP or HTTPS. If Nomad clients and Content Distribution are configured to use HTTP/S, Nomad clients using SSD register and query for content. | No, for communications with CM components. Nomad service on startup reads the configured ports from CM client registry and uses the same for LSZ generation. Yes, for communications with Tachyon Platform using Nomad's PlatformURL setting. |
TCP 5080 (HTTP) or TCP 5443 (HTTPS) | Default HTTP port to use for peer copy. If you are using a custom port, ensure that all agents use the same custom port. From Nomad 6.2, peer copy can be enabled over HTTP (default 5080) or HTTPS (default 5443). You can customize the ports for this feature in the host registry but a change to the default impacts Nomad's peer backup assistant which is used to capture user data on remote peers during OS deployments. | Yes, during installation. |
TCP 139 (SMB) and TCP 445 (SMB over TCP) | Required only if SMB is enabled. Used for peer-to-peer content transfer between the Nomad master and Nomad peers. Communications depend on how the DP is configured. That is HTTP, HTTPS, SMB or SMB over TCP. For Configuration Manager the default is HTTP or HTTPS. Windows Firewall automatically adds the exception when you enable File and Print Sharing but you may have to do this manually if you are using a different firewall product. | No. SMB ports cannot be configured. |
TCP 137 (SMB) and TCP 139 (SMB) | Required only if SMB is enabled. Used by SMB for data transfer and related communications. It is used to resolve NetBIOS names during a transfer. UDP NetBIOS name query packets are sent to this port. Windows Firewall automatically adds the exception when you enable File and Print Sharing but you may have to do this manually if you are using a different firewall product. | No. SMB ports cannot be configured. |
Nomad can use ephemeral ports (not discussed here). Ephemeral or high ports can either be UDP or TCP depending on the protocols used and are used to send information out. In a typical client-server communication, these are ports opened by the client on its own machine in order to send something to the server and they are closed as soon as the transmission is done, hence the term ephemeral. From a security perspective, it is not an issue.
Most firewalls will allow outgoing communications by default so in all likelihood, you will not need to do any firewall configuration. However, if your firewall blocks these outbound communications, consult the documentation for your firewall on how to enable these types of communications.
Basic Nomad architecture
Click image to enlarge.
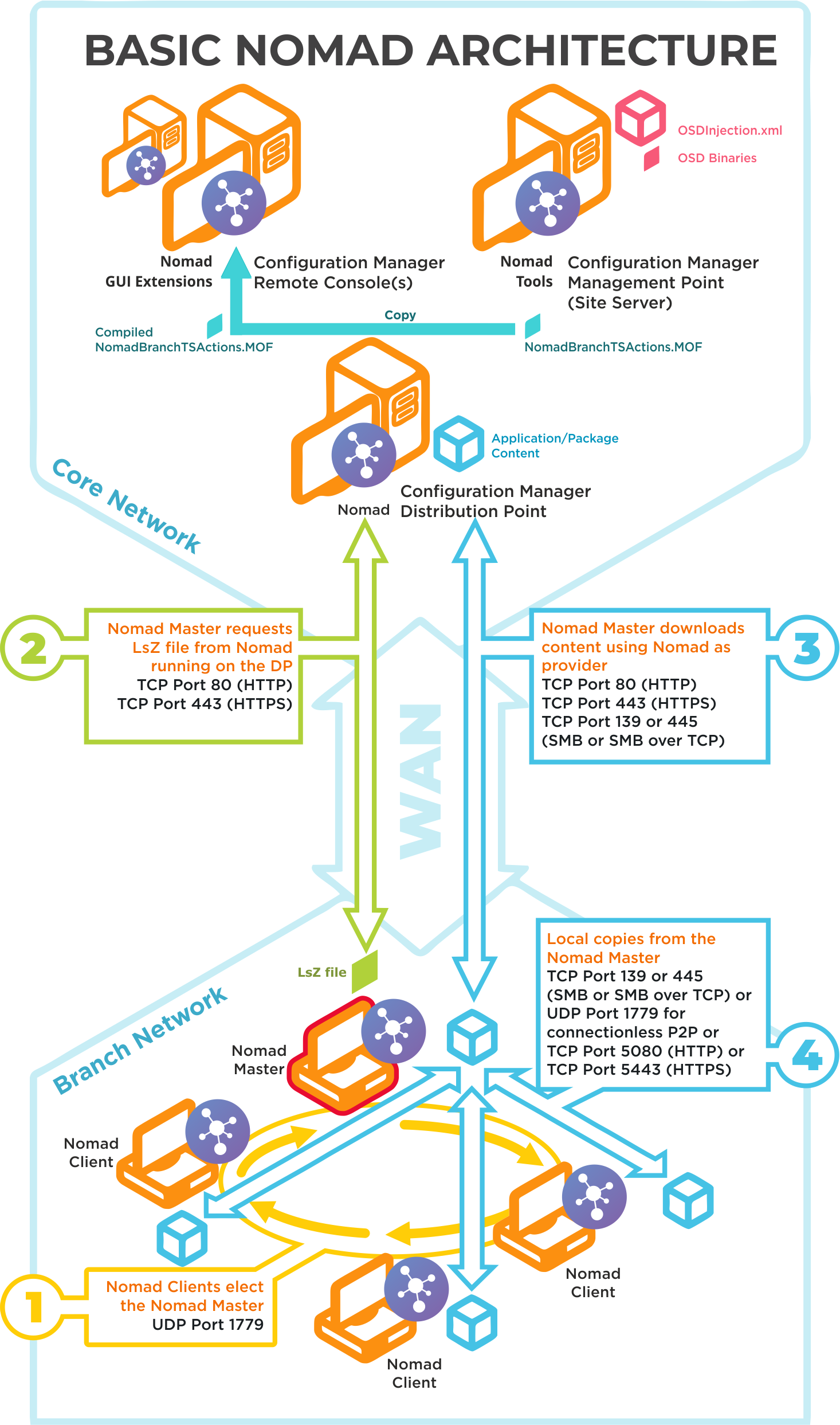
Ports | Notes |
|---|---|
UDP 1779 | Step 1By default, Nomad uses UDP Port 1779 to communicate during the election process for determining the master on a subnet. The Nomad installer will automatically add The default value for the port may be changed at install time using the MODULE.NOMAD.P2PPORT installer property or post-installation by changing the P2P_Port registry value. If you change the default port, you must ensure all Nomad clients communicate using the same port. The Nomad port (by default UPD Port 1779) must be open on all wireless access points to facilitate Nomad peer-to-peer communications. Not all vendors enable this port by default, please refer to the specific device vendor's documentation for details on how to enable ports on each WAP device. |
TCP 80 (HTTP) TCP 443 (HTTPS) | Step 2Nomad Master requests LSZ file from Nomad running on the DP. |
TCP 80 (HTTP) TCP 443 (HTTPS) TCP 139 (SMB) TCP 445 (SMB over TCP) | Step 3Nomad Master downloads content using Nomad as provider. This communication depends on how the DP is configured. It may be one of the following:
For Configuration Manager the default setting is HTTP or HTTPS. |
TCP 139 (SMB) TCP 445 (SMB over TCP) UDP 1779 (used for connectionless P2P) TCP 5080 (HTTP) TCP 5443 (HTTPS) | Step 4Local copies from the Nomad master. The recommended way to facilitate Nomad cache access is to enable Windows File and Print Sharing. If this is not feasible on your network environment you can configure Nomad to use different means to access network shares, see Nomad cache for more details on configuring this option. Connections may use one of the following:
|
Nomad pre-caching architecture and ports
Click image to enlarge.
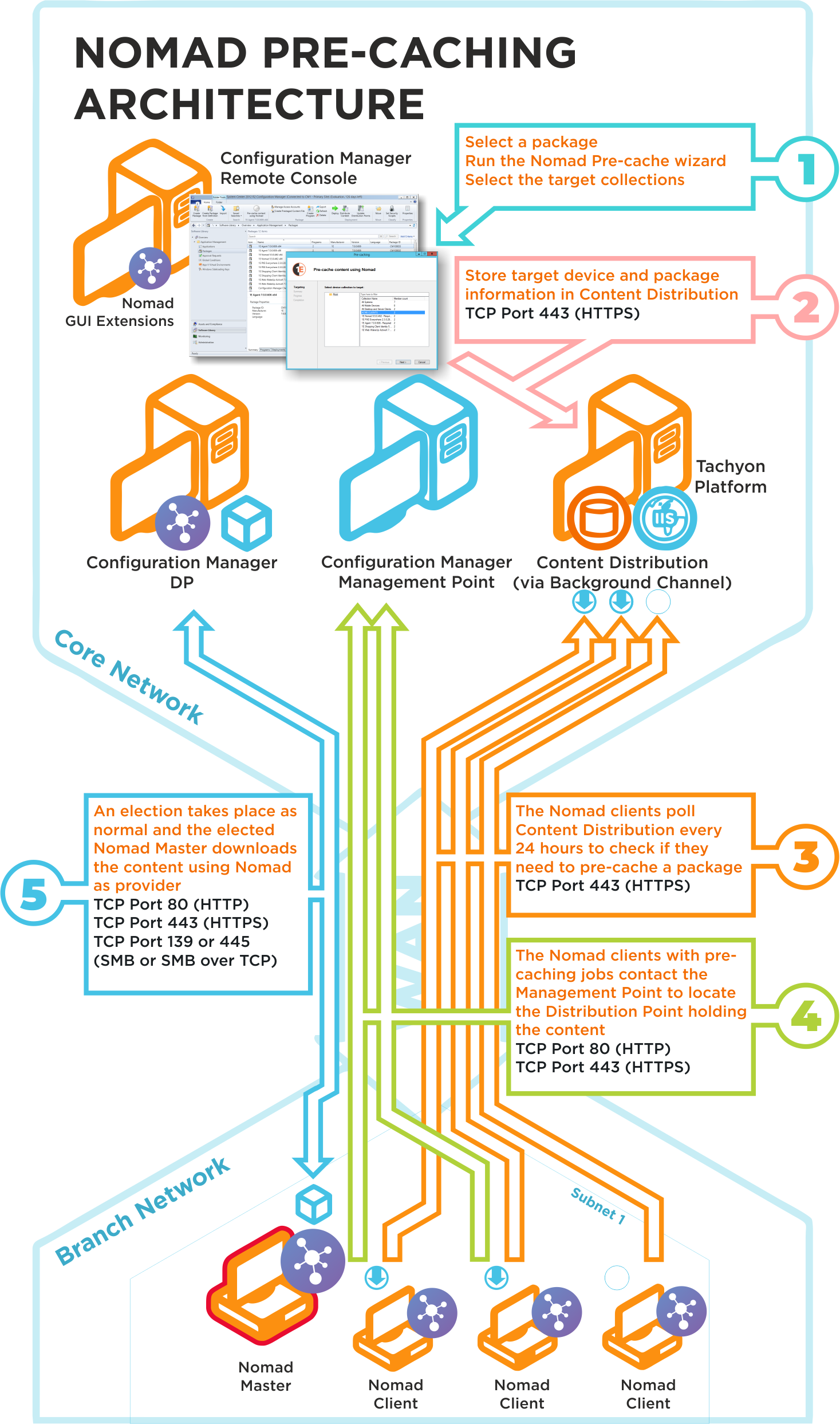
The Nomad pre-caching uses the following ports in its communications. If a site server is configured to use custom ports, pre-caching will use those ports to communicate with a management or distribution points. To ensure high-availability, pre-caching falls back to next available site server if it fails to communicate with a management or distribution point.
Ports | Description |
|---|---|
N/A | Step 1Choose a package and run the Nomad pre-caching wizard, selecting the target device collection. This step does not require any port configuration but the Nomad Configuration Manager console extensions must be installed in the Configuration Manager Console. |
TCP 80 (HTTP) TCP 443 (HTTPS) | Step 2The Nomad pre-caching wizard stores the target device and package information in Tachyon. |
TCP 80 (HTTP) TCP 443 (HTTPS) | Step 3The Nomad clients, where the pre-cache feature has been enabled, poll Tachyon every 24 hours to see if they need to pre-cache some content. This takes the form of pre-caching notifications that tell the Nomad clients they need to process a download job to fetch the specified content. |
TCP 80 (HTTP) TCP 443 (HTTPS) | Step 4The Nomad clients, with pre-caching notifications, contact the Management Point to locate the Distribution Point that holds the content. This may use HTTP or HTTPS depending on how the Management Point is configured. |
TCP 80 (HTTP) TCP 443 (HTTPS) TCP 139 (SMB) TCP 445 (SMB over TCP) | Step 5A Nomad Master election takes place and the elected master processes the job by downloading the pre-cache content using Nomad as provider. This is then distributed locally to the Nomad peers that also require the pre-cached content. This communication depends on how the DP is configured. It may be one of the following:
For Configuration Manager the default setting is either HTTP or HTTPS. |
Nomad and WakeUp integration architecture and ports
Click image to enlarge.
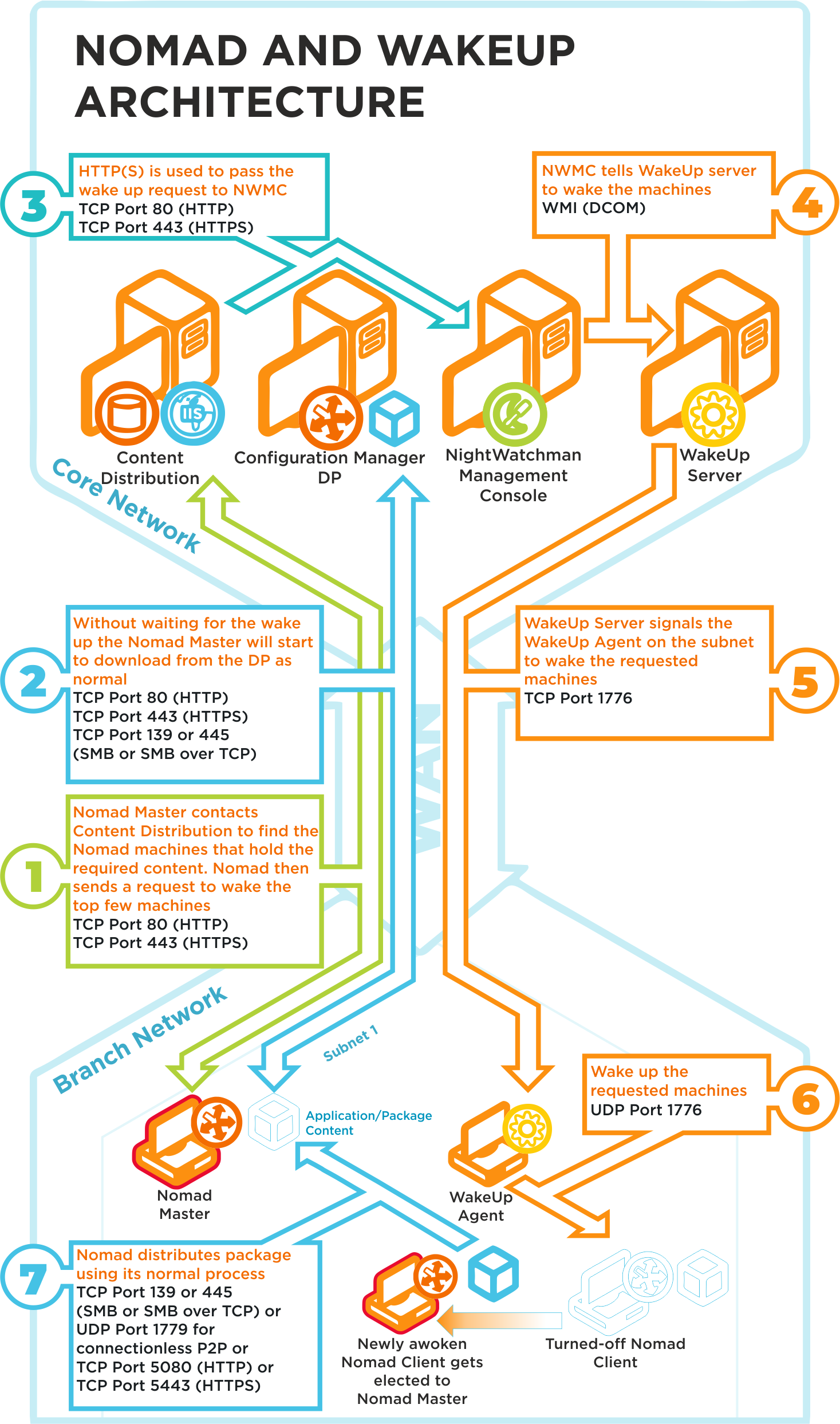
Ports | Description |
|---|---|
TCP 80 (HTTP) TCP 443 (HTTPS) | Step 1Nomad Master contacts Content Distribution and gets a list of Nomad devices that hold the content it requires. Nomad sends a request to wake the top 5 devices on the list. Refer to WakeUpBatchSize for details about how you can set the maximum number of machines to wake up in a single call. |
TCP 80 (HTTP) TCP 443 (HTTPS) TCP 139 (SMB) TCP 445 (SMB over TCP) | Step 2Without waiting for any devices to be awoken, the Nomad master starts to download content from the DP. This communication depends on how the DP is configured. It may be one of the following:
For Configuration Manager, the default setting is HTTP or HTTPS. |
TCP 80 (HTTP) TCP 443 (HTTPS) | Step 3Content Distribution posts the wake message from Nomad to the NightWatchman Management Center Web API. |
WMI (DCOM) | Step 4NightWatchman Management Center tells the WakeUp server to wake the requested devices. |
TCP 1776 | Step 5WakeUp Server signals the WakeUp Agent on the appropriate subnet to wake the requested devices. |
UDP 1776 | Step 6The WakeUp agent on the subnet sends a wakeup request to the requested devices. |
TCP 139 (SMB) TCP 445 (SMB over TCP) UDP 1779 (connectionless P2P) | Step 7As part of its standard behavior, Nomad holds regular elections (every 5 minutes) to determine the most appropriate master. If a device is found (i.e. one that has been recently awoken) that holds more of the required content, it stops downloading from the DP and fetches the content from the new device's cache. This may be via SMB or via connectionless P2P, depending on the configuration of Nomad. |
Nomad SSD architecture and ports
Click image to enlarge.
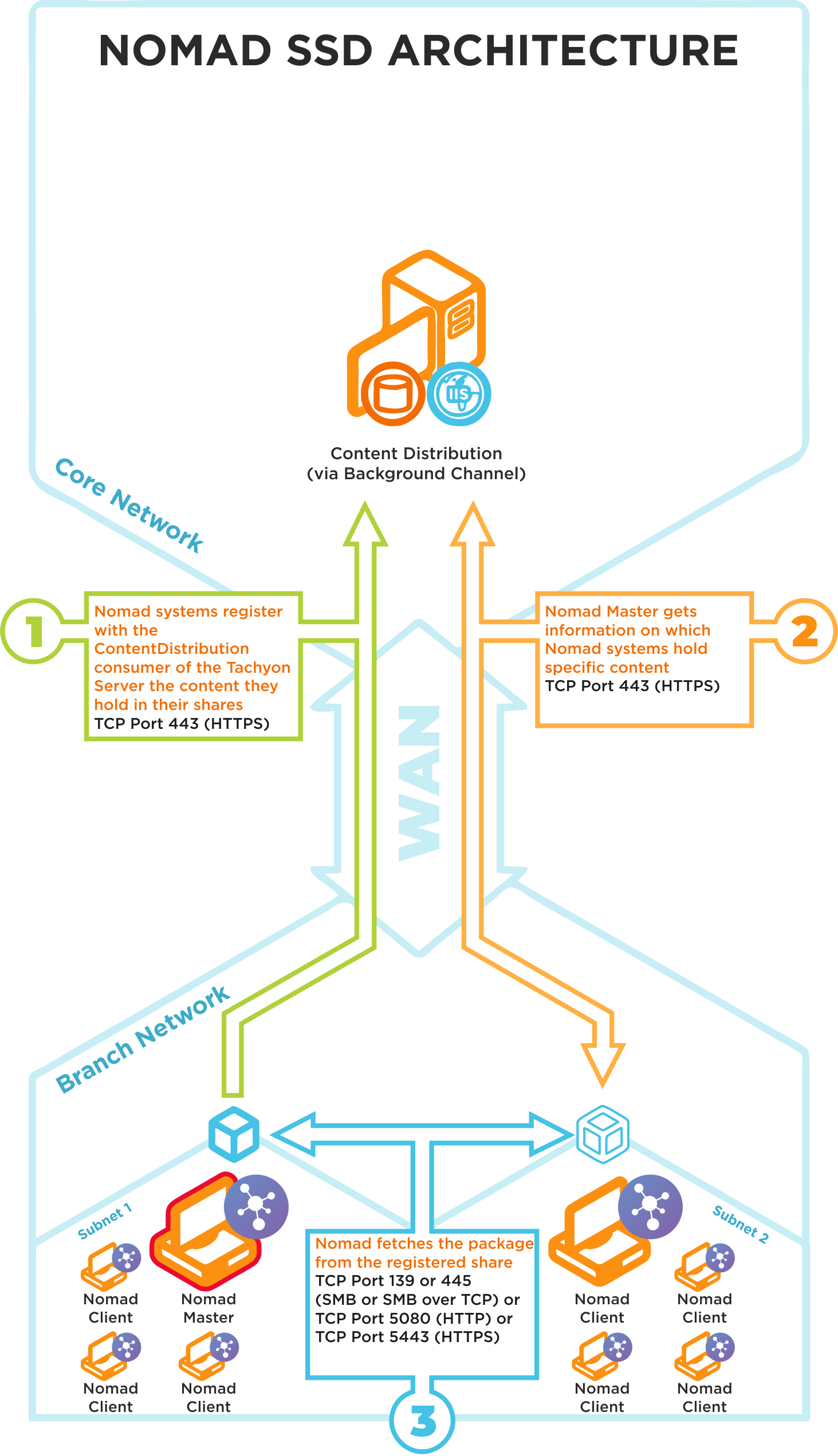
Nomad SSD uses the following ports in its communications:
Ports | Notes |
|---|---|
TCP 80 (HTTP) TCP 443 (HTTPS) | Step 1Nomad systems on the branch site register in Content Distribution the content they hold in their shares |
TCP 80 (HTTP) TCP 443 (HTTPS) | Step 2Nomad Masters get information on which Nomad systems hold specific content |
TCP 80 (HTTP) TCP 443 (HTTPS) TCP 139 (SMB) TCP 445 (SMB over TCP) | Step 3Nomad Master fetches a package from the registered Nomad share on a neighboring subnet |
We recommend that the latest version of Tachyon Platform is installed to support this feature, please refer to Requirements for more details.